In today’s digital world, protecting your business from cyber threats is more critical than ever. At DPRS Lab, we provide comprehensive Cyber Security Services designed to safeguard your data, systems, and networks from ever-evolving threats. From proactive threat detection to incident response and recovery, we ensure your business stays secure and resilient against cyberattacks.
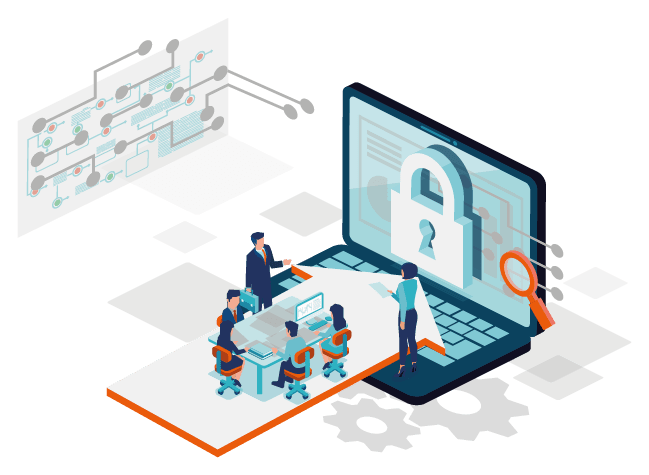
Cyber threats are becoming more sophisticated, and businesses need robust, proactive security strategies to stay protected. DPRS Lab offers cutting-edge Cyber Security Services that address the unique challenges your business faces. Here’s why we’re your ideal partner for safeguarding your digital assets:
Our security solutions cover all aspects of your business, from network defense to data protection and endpoint security.
We use advanced tools and techniques to identify vulnerabilities and prevent cyberattacks before they happen.
We understand that every business has unique needs. Our solutions are customized to fit your specific security requirements and business goals.
Our team consists of seasoned security professionals who have hands-on experience with the latest cyber threats and technologies.
We provide 24/7 monitoring and support to ensure your systems remain secure around the clock.
Network security is the first line of defense against cybercriminals. We help protect your internal and external networks from unauthorized access and attacks.
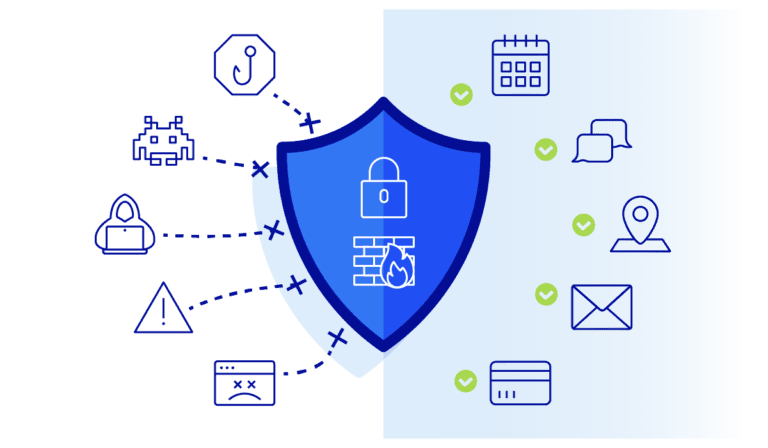
Endpoints are often the weakest link in your security chain. We protect your devices, including laptops, desktops, and mobile devices, from malware, ransomware, and other threats.

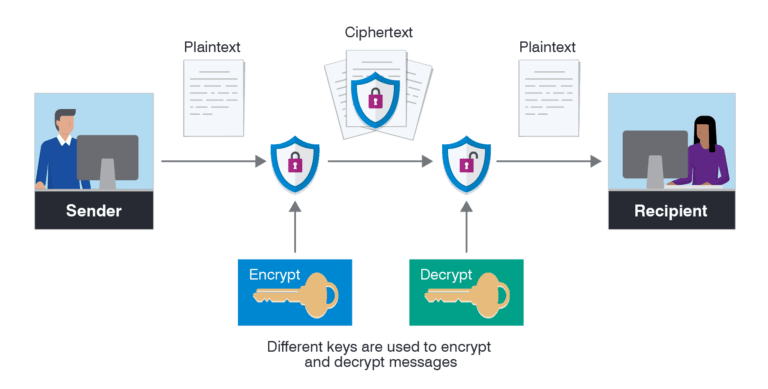
Data is one of your most valuable assets, and we ensure that it is protected against theft, loss, or unauthorized access.
Identifying vulnerabilities before attackers do is crucial for maintaining a secure network. We help you proactively address weaknesses before they can be exploited.

In the event of a breach, it’s essential to act quickly and efficiently. We provide incident response services to contain and recover from attacks while minimizing damage.
Your employees are often the first line of defense against cyber threats. We offer training programs to help them recognize and respond to security risks.

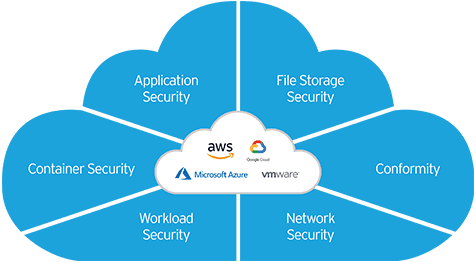
As businesses increasingly move to the cloud, ensuring the security of cloud environments is paramount. We help you secure your cloud infrastructure to safeguard your data and applications.
Cybersecurity isn’t just about protection; it’s also about complying with regulations and managing risk.


Your business deserves the best in Cyber Security. Don’t leave your digital assets unprotected. Contact DPRS Lab today to learn more about our Cyber Security Services and how we can safeguard your business against evolving threats. Let us help you build a strong, resilient security framework that keeps your data safe and your business secure.